Mastering Vulnerability Scanning: Enhancing Cybersecurity
Vulnerability scanning is a key tool in cybersecurity. It helps find weak spots in computer systems that hackers might exploit. In today’s digital world, it’s crucial for keeping data safe.
Brief Overview of Vulnerability Scanning
Vulnerability scanning involves using special software to check for weaknesses in networks and computers. It’s like a health check-up for your computer systems, looking for any areas that need fixing to prevent cyber attacks.
Importance in the Current Cybersecurity Landscape
In our world full of technology, cybersecurity is more important than ever. Vulnerability scanning plays a big role in this. It helps businesses and individuals stay one step ahead of hackers, protecting sensitive information from being stolen or damaged.
Understanding Vulnerability Scanning
Vulnerability scanning is a process that helps find security issues in computer systems and networks. It’s like a detective searching for clues to stop cyber criminals. This section explains what vulnerability scanning is and how it works.
What is Vulnerability Scanning?
Vulnerability scanning is a way to check computers and networks for security risks. It uses software that scans systems to find any weak spots that hackers could use to get in. Think of it like a security guard checking for unlocked doors in a building.
- How it works: The scanning software looks at how the system is set up and compares it to a list of known security issues.
- What it finds: It can spot things like outdated software, weak passwords, and unprotected files.
How Vulnerability Scanning Works
The process of vulnerability scanning involves several steps:
- Preparation: Deciding which parts of the network or system need to be checked.
- Scanning: The software scans these parts and looks for known vulnerabilities.
- Reporting: It then creates a report that lists all the found issues.
- Analysis: Experts look at the report to understand how serious the issues are.
- Action: Finally, steps are taken to fix these issues and improve security.
Vulnerability scanning is a crucial part of keeping computer systems safe. It helps find problems before hackers can use them to cause harm. Regular scanning is important because new security risks can appear at any time.
The Benefits of Regular Vulnerability Scanning
Regular vulnerability scanning is like having a constant guard for your computer systems. It checks for dangers and helps keep your data safe. Let’s explore why doing these scans often is so beneficial.
Keeping Your Systems Safe
One of the main benefits of regular vulnerability scanning is keeping your systems safe. It’s like having a regular health check for your computer network.
- Finds Weaknesses: Scans find where your system might be easy to break into.
- Updates Security: It helps you know when to update or change things for better safety.
- Stops Hackers: By finding and fixing problems, it makes it harder for hackers to get in.
Staying Ahead of Threats
Regular scanning doesn’t just fix current problems; it also helps you stay ahead of new threats.
- New Threats: Hackers always find new ways to attack. Scanning regularly helps you keep up.
- Quick Fixes: When you know about problems quickly, you can fix them fast.
- Peace of Mind: Knowing your systems are checked regularly helps you feel more secure.
Regular vulnerability scanning is a key part of keeping your digital world safe. It’s an ongoing process that helps protect against both current and future cyber threats.
Types of Vulnerability Scans Explained
Vulnerability scans come in different types, each serving a unique purpose. Understanding these types helps you choose the right scan for your needs. Let’s break down the most common types of vulnerability scans.
Network-Based and Host-Based Scanning
Network-based and host-based scans are two important types of vulnerability scanning.
- Network-Based Scanning:
- What it does: Checks the security of your network.
- Why it’s important: Finds risks in how your computers talk to each other.
- Best for: Looking at the big picture of your network’s security.
- Host-Based Scanning:
- What it does: Focuses on individual computers or devices.
- Why it’s important: Finds risks in specific computers or servers.
- Best for: Deep checks on single systems.
Web Application and Database Scanning
Scans for web applications and databases are essential due to their frequent targeting by hackers.
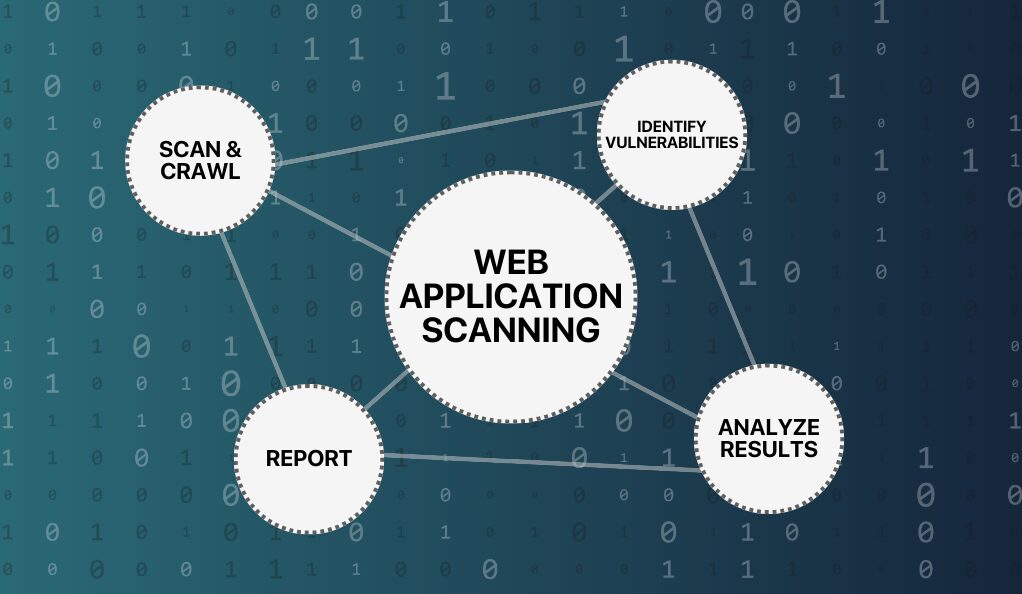
Web Application Scanning:
This tool scans websites and web applications to identify security vulnerabilities. Its crucial role lies in safeguarding online services and sensitive data, making it indispensable for businesses that operate web-based services or online stores.
Database Scanning:
This tool assesses databases for potential vulnerabilities, playing a vital role in ensuring the security of sensitive information such as customer data. It is highly recommended for businesses that handle substantial data storage to proactively protect their valuable information assets.
Cloud Vulnerability Scanning
With many services moving to the cloud, this type of scanning is becoming more important.
- What it does: Finds security issues in cloud services and configurations.
- Why it’s important: Protects data and services that are stored online, not just on your own computers.
- Best for: Businesses using cloud storage or services.
Best Practices in Vulnerability Scanning
To get the most out of vulnerability scanning, it’s important to follow some best practices. These practices ensure that your scans are effective and your network stays secure.
Regular and Comprehensive Scanning
Consistent and thorough scanning is key to maintaining strong security.
- Frequency: Regular scans, like monthly or quarterly, help catch new vulnerabilities.
- Coverage: Make sure to scan all parts of your network, including less obvious areas.
- Updates: Keep your scanning tools updated for the latest threat detection.
Integrating Scans into Your Security Strategy
Vulnerability scanning should be part of a bigger security plan.
- Teamwork: Work with your security team to understand scan results and fix issues.
- Planning: Have a clear plan for what to do when a scan finds a problem.
- Learning: Use scan results to learn and improve your overall security measures.
Choosing the Right Vulnerability Scanning Tools
Selecting the right tools for vulnerability scanning is crucial. The right tools can make the difference in effectively protecting your network. Let’s look at what to consider when choosing these tools.
Key Features to Look For
When picking vulnerability scanning tools, focus on these features:
- Comprehensive Detection: The tool should spot a wide range of vulnerabilities.
- User-Friendly: It should be easy to use, even if you’re not a tech expert.
- Regular Updates: The tool must update regularly to catch new types of threats.
- Good Support: Look for tools with strong customer support for help when needed.
Balancing Comprehensiveness and Usability
Finding a tool that’s both thorough and easy to use is important.
- Thoroughness: The tool should do deep scans to find as many vulnerabilities as possible.
- Ease of Use: It shouldn’t be too complex or confusing to operate.
- Speed: Consider how fast the tool can complete scans without affecting your network’s performance.
Vulnerability Scanning vs. Penetration Testing
Understanding the difference between vulnerability scanning and penetration testing is important. Both are useful, but they serve different purposes in cybersecurity.
What is Vulnerability Scanning?
Vulnerability scanning is about finding potential security issues.
- Automated: It uses software to automatically find weaknesses.
- Surface-Level: Scans provide a general overview of security health.
- Regular Use: Best for frequent checks to catch new or missed vulnerabilities.
What is Penetration Testing?
Penetration testing goes deeper to see how strong your security really is.
- Manual: It involves experts actively trying to break into your systems.
- In-Depth: This test looks for specific ways hackers could exploit vulnerabilities.
- Occasional Use: Best done at regular intervals, like annually, or after major changes.
Vulnerability scanning is like a regular health check-up, while penetration testing is like a thorough examination of specific problems. Both are important for a complete cybersecurity strategy. Scanning regularly finds potential issues, and penetration testing explores how serious those issues might be.
Implementing Effective Vulnerability Management
Effective vulnerability management is more than just running scans. It’s about taking action based on what those scans find. Let’s explore how to manage vulnerabilities effectively.
Steps to Manage and Remediate Identified Vulnerabilities
Managing vulnerabilities involves several key steps:
- Identify Vulnerabilities: Use scanning tools to find security weaknesses.
- Prioritize Issues: Decide which vulnerabilities to fix first, based on their risk.
- Plan Remediation: Create a plan for how to fix these vulnerabilities.
- Take Action: Follow the plan to fix the issues.
- Verify Fixes: Run scans again to make sure the vulnerabilities are truly fixed.
- Repeat Regularly: Keep scanning and fixing new vulnerabilities as they appear.
Importance of a Top-Down Approach in Organizations
A top-down approach means getting everyone, from top management to everyday users, involved in cybersecurity.
- Leadership Support: Management should understand and support cybersecurity efforts.
- Policy and Training: Create clear security policies and train staff on them.
- Continuous Improvement: Always look for ways to make your cybersecurity better.
Conclusion
Vulnerability scanning is a vital defense in cybersecurity, acting as a vigilant guard against potential threats. It’s essential for identifying weaknesses, preventing cyber attacks, and maintaining robust security. Staying safe online requires ongoing effort: staying informed about cybersecurity trends, being proactive in defense strategies, and ensuring everyone in your organization understands their role in data protection. Remember, effective cybersecurity is a continuous journey, and regular vulnerability scanning is a key step in navigating this path safely and successfully.

Leave a Reply