How to Encrypt Files on Your Personal Computer: A Comprehensive Guide
In today’s digital age, the security of our personal and professional data on PCs has never been more crucial. File Encryption on PC is a vital tool to combat the increasing threats from hackers, malware, and other cyber-attacks. Ensuring the confidentiality and integrity of our files is paramount, and this is where file encryption comes into play.
What is File Encryption?
File encryption is a security method where information is encoded and can only be accessed or decrypted by a user with the correct encryption key. In simpler terms, it’s like locking your files in a digital safe. Even if someone were to access the encrypted data, without the right key, the information would appear as a jumbled mess, rendering it useless.
Why is File Encryption Essential?
- Confidentiality: Whether it’s personal photos, financial documents, or business contracts, encryption ensures that only authorized individuals can access your files.
- Integrity: Encryption ensures that your files remain unaltered and free from unauthorized changes. If someone tries to tamper with the encrypted data, it will become corrupted and unreadable.
- Protection Against Threats: With the rise of ransomware attacks, where hackers encrypt your files and demand a ransom to unlock them, having your data already encrypted can act as a layer of protection.
Data in Transit vs. Data at Rest
- Data in Transit: This refers to data actively moving from one location to another, such as over the internet or through a private network. Examples include sending an email, transferring money online, or even browsing a website. Encryption ensures that this data remains secure as it travels, preventing interception or tampering.
- Data at Rest: This pertains to data stored on physical or virtual devices, like hard drives, servers, or cloud storage. Encrypting data at rest ensures that even if someone were to gain physical access to your storage medium, they wouldn’t be able to read the data without the encryption key.
Understanding Cryptography Basics
Cryptography, often synonymous with encryption, is the science of securing information by converting it into a code. This ensures that only someone with the right key can decipher it. To truly grasp the essence of file encryption, it’s essential to understand the foundational elements of cryptography.
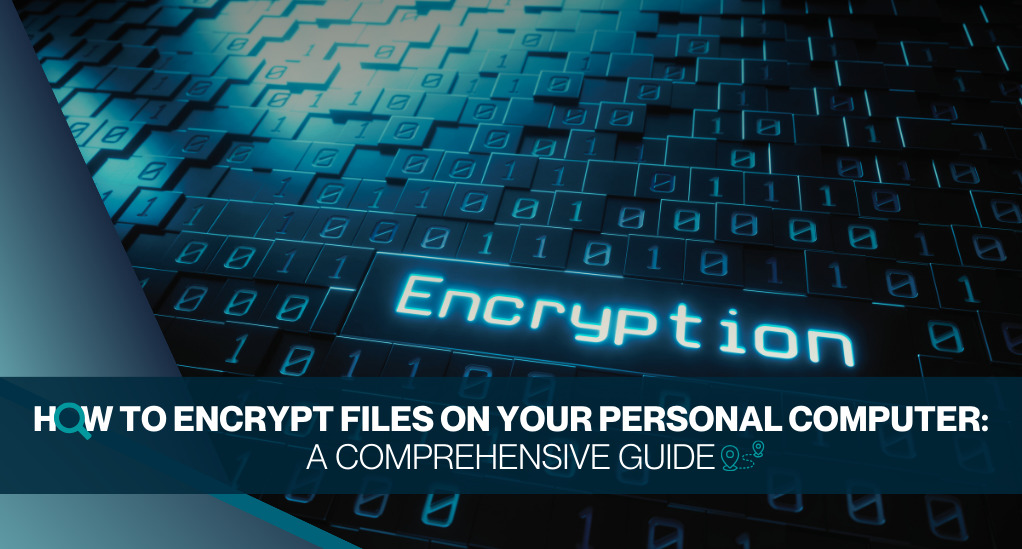
Symmetric vs. Asymmetric Encryption: What’s the Difference?
At the heart of cryptography are two primary types of encryption: symmetric and asymmetric.
- Symmetric Encryption: Here, a single key is used both for encrypting the original data and decrypting the encoded data. Think of it as a single key that locks and unlocks a box. While symmetric encryption is faster and more efficient, its main challenge lies in the key’s distribution. If someone intercepts the key during its transfer, they can decrypt any data encrypted with it.
- Asymmetric Encryption: This method uses two keys: a public key for encryption and a private key for decryption. The public key is shared openly, allowing anyone to encrypt data with it. However, only the person with the corresponding private key can decrypt it. This method is more secure for data transmission over the internet, but it’s slower than symmetric encryption due to its complexity.
Public Key Infrastructure (PKI) and Its Role in Encryption
Public Key Infrastructure (PKI) is a combination of hardware, software, policies, and standards that work together to provide a framework for secure communications. It’s the backbone of many security services, including digital signatures and data encryption.
The primary purpose of PKI is to manage digital keys and certificates. Digital certificates verify the owner of a public key, ensuring that the key belongs to the person it claims to. This way, when someone encrypts data with a public key, they can be confident that only the intended recipient, who has the corresponding private key, can decrypt it.
Key Takeaways:
- Encryption is the bedrock of secure digital communication, ensuring data remains confidential and retains its integrity.
- Choosing between symmetric and asymmetric encryption depends on the specific use case, with each having its advantages and drawbacks.
- PKI plays a pivotal role in managing and distributing digital keys, ensuring that encrypted data reaches its intended recipient securely.
Methods of File Encryption
As we delve deeper into the realm of securing digital data, it becomes evident that there isn’t a one-size-fits-all approach. Different scenarios and requirements demand various encryption methods. In this section, we’ll explore the predominant techniques and how they function.
Software Encryption: How Does It Work?
Software encryption involves using computer programs to convert data into a code to prevent unauthorized access. This software uses algorithms, which are complex mathematical procedures, to turn readable data (plaintext) into an unreadable format (ciphertext) and vice versa.
There are two primary types of ciphers used in software encryption:
- Public Key Ciphers (Asymmetric Ciphers): As previously discussed, these use two keys: a public key for encryption and a private key for decryption. It’s the backbone of many online transactions and communications.
- Symmetric Key Ciphers: These use a single key for both encryption and decryption. The challenge lies in securely sharing the key between parties.
Stream Ciphers vs. Block Ciphers: A Comparative Analysis
- Stream Ciphers: These encrypt data one bit or byte at a time, making them suitable for real-time communications like audio and video streaming. The key initializes a keystream generator, and its output encrypts the plaintext.
- Block Ciphers: These algorithms split the plaintext into fixed-size blocks, encrypting one block at a time. For instance, the AES (Advanced Encryption Standard) processes 16-byte blocks, while its predecessor, DES (Data Encryption Standard), encrypted 8-byte blocks.
Tools and Techniques for File Encryption
While understanding the underlying methods is crucial, it’s equally important to know the tools available for implementing these techniques:
- Full Disk Encryption: As the name suggests, this encrypts the entire disk, except for the bits necessary for booting. It ensures that if someone gains physical access to your computer, they can’t access the data without the encryption key.
- Partition Encryption: This focuses on encrypting individual disk partitions. It’s useful when you want to secure specific sections of your storage.
- File System-Level Encryption: Here, entire file systems, composed of one or more partitions, are encrypted. It’s a more granular approach, allowing for specific folders or files to remain unencrypted if desired.
- Application-Level Encryption: This involves encrypting data within specific applications, like databases. The application itself handles the encryption and decryption processes.
Encrypting Data in Transit
As we increasingly rely on digital communications, ensuring the security of data as it travels between devices or across networks becomes paramount. Data in transit is especially vulnerable because it moves openly, making it an attractive target for cybercriminals. In this section, we’ll explore the intricacies of securing data in transit.
Why is Data in Transit Vulnerable?
When data moves between two endpoints, such as from your computer to a server or between two servers, it traverses multiple networks. These can be secure internal networks or the vast expanse of the internet. At any point during this journey, without proper encryption, data can be:
- Intercepted: Cybercriminals can ‘eavesdrop’ on the data, capturing sensitive information.
- Modified: Unauthorized changes can be made to the data, leading to misinformation or malicious activities.
- Redirected: Data can be rerouted to a different destination, causing delays or misdeliveries.
Popular Methods for Encrypting Data in Transit
Several protocols and tools have been developed to ensure the secure transmission of data. Here’s a breakdown of some of the most widely used methods:
- IPsec (Internet Protocol Security): A suite of protocols that encrypts and authenticates data at the IP layer. It’s commonly used in virtual private networks (VPNs) to secure internet traffic.
- SCP (Secure Copy Protocol): Used for securely transferring computer files between a local and a remote host or between two remote hosts.
- SFTP (Secure File Transfer Protocol): An extension of the Secure Shell protocol (SSH) that provides secure file transfer capabilities.
- SSH (Secure Shell): A cryptographic network protocol for operating network services securely over an unsecured network. It’s widely used for remote server login and command execution.
- OpenPGP: A data encryption and decryption program that provides cryptographic privacy and authentication. It’s often used for securing emails.
- HTTPS (HyperText Transfer Protocol Secure): This HTTP extension provides secure web browsing. It encrypts the data traveling between the user’s browser and the web server.
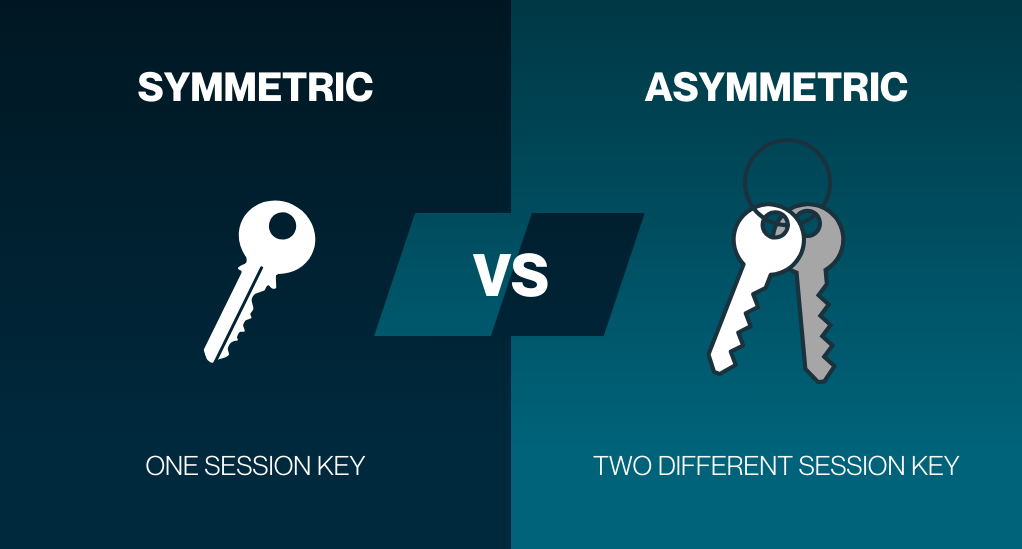
Ensuring Secure Connections with PKI
Public Key Infrastructure (PKI) plays a pivotal role in establishing secure connections. When data is in transit between two entities that might not know each other, like visiting a website, PKI comes into play. It involves:
- Digital Certificates: These confirm the public key’s owner and ensure data reaches the correct recipient.
- Certificate Authorities (CAs): Trusted entities that issue digital certificates.
- Key Exchange: After establishing a secure connection with PKI, endpoints can share a symmetric key to speed up encryption and decryption.
Securing Data at Rest
While ensuring the security of data as it moves is crucial, equally important is the protection of data that remains stationary or “at rest.” This refers to all the information stored in databases, hard drives, memory sticks, or any other form of digital storage. Given that this data isn’t actively moving, one might assume it’s safe. However, data at rest is a prime target for cyberattacks, making its protection indispensable.
Why Protect Data at Rest?
- Physical Threats: Devices can be stolen or lost. Without encryption, anyone with access to the device can access the data.
- Unauthorized Access: Even within secure networks, there’s a risk of unauthorized personnel accessing sensitive data.
- Compliance and Regulations: Many industries have regulations requiring the protection of sensitive data. Encrypting data at rest helps organizations meet these requirements.
Layers of Encryption for Data at Rest
Data at rest can be encrypted at various layers in the storage stack, each offering a different level of protection:
- Disk Layer: Known as Full Disk Encryption (FDE), this method encrypts the entire hard drive. Everything, including the operating system and applications, is encrypted, except for the booting files.
- Partition Layer: Here, individual sections or partitions of a disk are encrypted. It’s useful when different partitions have varying security requirements.
- Volume Layer: This involves encrypting a combination of disks or partitions, known as a volume. It’s a more flexible approach, allowing for varying encryption levels within a single storage device.
- File System Layer: This encrypts entire file systems. Users can choose to encrypt specific directories, ensuring that files within those directories are secure.
- Application Layer: This is the most granular form of encryption, where specific applications, like databases, handle the encryption process. Only data used by the application is encrypted, leaving other data on the device unprotected.
| Encryption Layer | Description | Use Cases |
|---|---|---|
| Disk Layer | Encrypts the entire disk | Personal laptops, mobile devices |
| Partition Layer | Encrypts specific disk partitions | Multi-user systems, servers |
| Volume Layer | Encrypts combined disks or partitions | External storage devices, network storage |
| File System Layer | Encrypts entire file systems or directories | Shared systems, cloud storage |
| Application Layer | Encrypts data within specific applications | Databases, enterprise software |
Choosing the Right Encryption Method
The choice of encryption layer depends on several factors:
- Sensitivity of Data: Highly confidential data might require multiple layers of encryption, while less sensitive data might only need file system or application-level encryption.
- Performance Impact: While encryption ensures data security, it can also impact system performance. For instance, full disk encryption might slow down system boot times.
- User Accessibility: If multiple users need access to the data, file system or application-level encryption might be more appropriate.
Tools and Software for File Encryption
In the digital age, the tools we use play a pivotal role in determining the strength and efficiency of our encryption efforts. With a plethora of software options available, choosing the right one can be daunting. This section aims to provide an overview of popular encryption tools, their features, and guidance on selecting the most suitable one for your needs.
Popular File Encryption Software
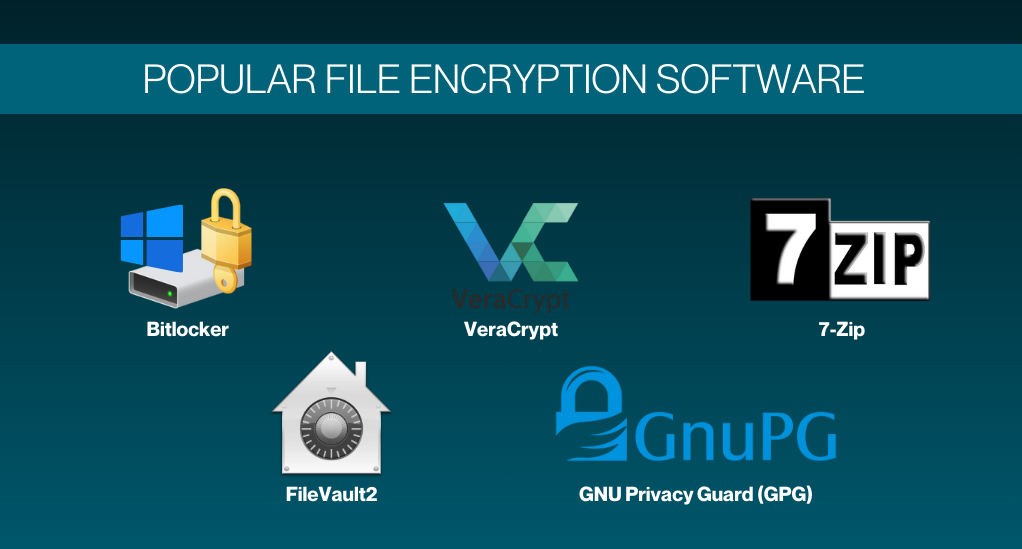
- BitLocker:
- Platform: Windows
- Description: A full disk encryption program that integrates with the operating system. It encrypts the entire drive, ensuring data is protected from theft or unauthorized access.
- Key Features: TPM (Trusted Platform Module) support, multiple authentication modes, and integration with Active Directory.
- FileVault 2:
- Platform: macOS
- Description: Apple’s solution for full disk encryption. It uses the user’s login password as the encryption passphrase.
- Key Features: XTS-AES-128 encryption, automatic encryption of saved files, and seamless integration with macOS.
- VeraCrypt:
- Platform: Windows, macOS, Linux
- Description: An open-source disk encryption software that can create a virtual encrypted disk or encrypt an entire partition.
- Key Features: Strong encryption algorithms, hidden volumes, and cross-platform support.
- GNU Privacy Guard (GPG):
- Platform: Windows, macOS, Linux
- Description: A free alternative to the PGP suite of cryptographic software. It’s primarily used for securing emails.
- Key Features: Public key cryptography, digital signatures, and compatibility with PGP.
- 7-Zip:
- Platform: Windows, Linux (through p7zip)
- Description: While primarily a file archiver, 7-Zip offers strong AES-256 encryption for file compression.
- Key Features: High compression ratio, integrated file manager, and open-source.
Choosing the Right Encryption Tool
When selecting an encryption tool, consider the following factors:
- Purpose: Are you looking to encrypt individual files, emails, or an entire disk? Different tools cater to different needs.
- Platform Compatibility: Ensure the software is compatible with your operating system.
- Usability: User-friendly interfaces can make the encryption process smoother, especially for those new to the field.
- Strength of Encryption: Choose tools with robust encryption algorithms that the cybersecurity community endorses.
- Cost: While many excellent free tools are available, some premium software might offer additional features worth the investment.
Best Practices and Performance Considerations
As we approach the culmination of our exploration into file encryption, it’s essential to emphasize that merely employing encryption tools isn’t enough. How you use these tools directly affects their effectiveness. This section will shed light on best practices to ensure optimal encryption performance and highlight common pitfalls to avoid.
Best Practices for File Encryption
- Regularly Update Software: Encryption tools, like all software, receive updates to patch vulnerabilities and enhance performance. Regularly updating ensures you benefit from the latest security measures.
- Use Strong, Unique Passwords: The strength of your encryption often depends on the robustness of your password. Utilize a combination of letters, numbers, and symbols, and avoid using easily guessable information.
- Backup Encryption Keys: Losing access to your encryption key can mean losing access to your data. Store backup copies of your keys in secure locations, both digitally and physically.
- Multi-Factor Authentication (MFA): Enhance security by requiring multiple forms of verification before granting access. This could be something you know (password), something you have (a physical device), or something you are (biometric verification).
- Regularly Audit and Monitor Access: Periodically review who has access to your encrypted data. Remove access for those who no longer need it and monitor for any unauthorized attempts.
- Stay Informed: The world of cybersecurity is ever-evolving. Stay updated on the latest threats and advancements in encryption technology.
Performance Considerations
While encryption is paramount for security, it can have implications for system performance. Here are some considerations and tips:
- Encryption Overhead: Encryption processes can consume system resources, leading to slower performance. Choose tools optimized for your system’s specifications.
- Disk Space: Some encryption methods might increase the size of files or require additional disk space. Ensure you have adequate storage.
- Decryption Time: Accessing encrypted data requires decryption, which can introduce delays. For frequently accessed data, consider solutions with faster decryption times.
- Hardware-Based Encryption: Some modern CPUs offer hardware-based encryption features, which can significantly speed up the process without taxing system resources.
- Selective Encryption: Not all data requires the same level of security. Encrypt only sensitive data to balance between security and performance.
Common Pitfalls to Avoid
- Forgetting Passwords: If you forget the right password or encryption key, you risk losing your data forever. Use password managers or secure methods to store them.
- Over-reliance on Encryption: While encryption is a robust security measure, it should be part of a multi-layered security approach, including firewalls, anti-malware tools, and regular backups.
- Neglecting Physical Security: Strong encryption isn’t foolproof when someone has physical access to your device. Store devices securely and think about using full disk encryption for extra protection.
Conclusion
In the digital age, the security of our data, both in transit and at rest, is of paramount importance. Through this comprehensive exploration into file encryption, we’ve unveiled the intricacies of various encryption methods, tools, and best practices. By understanding and implementing these strategies, individuals and organizations can fortify their digital assets against ever-evolving cyber threats. As we navigate this interconnected world, it’s crucial to remember that proactive measures, continuous learning, and the right tools are our best allies in ensuring the confidentiality, integrity, and accessibility of our cherished data.